Adding IoT capabilities to products is full of challenges, without an clear Go-to IoT strategy, it will be a hard adventure
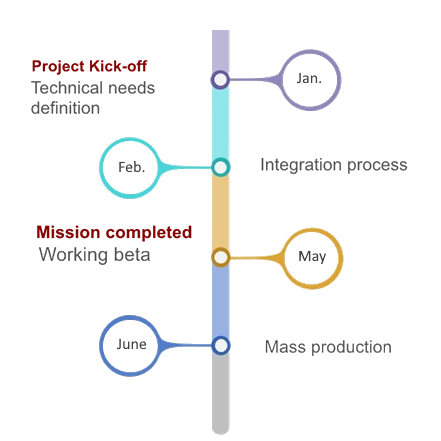
MindoLife IoT platform can dramatically reduce your time to market from more than a year to a several months
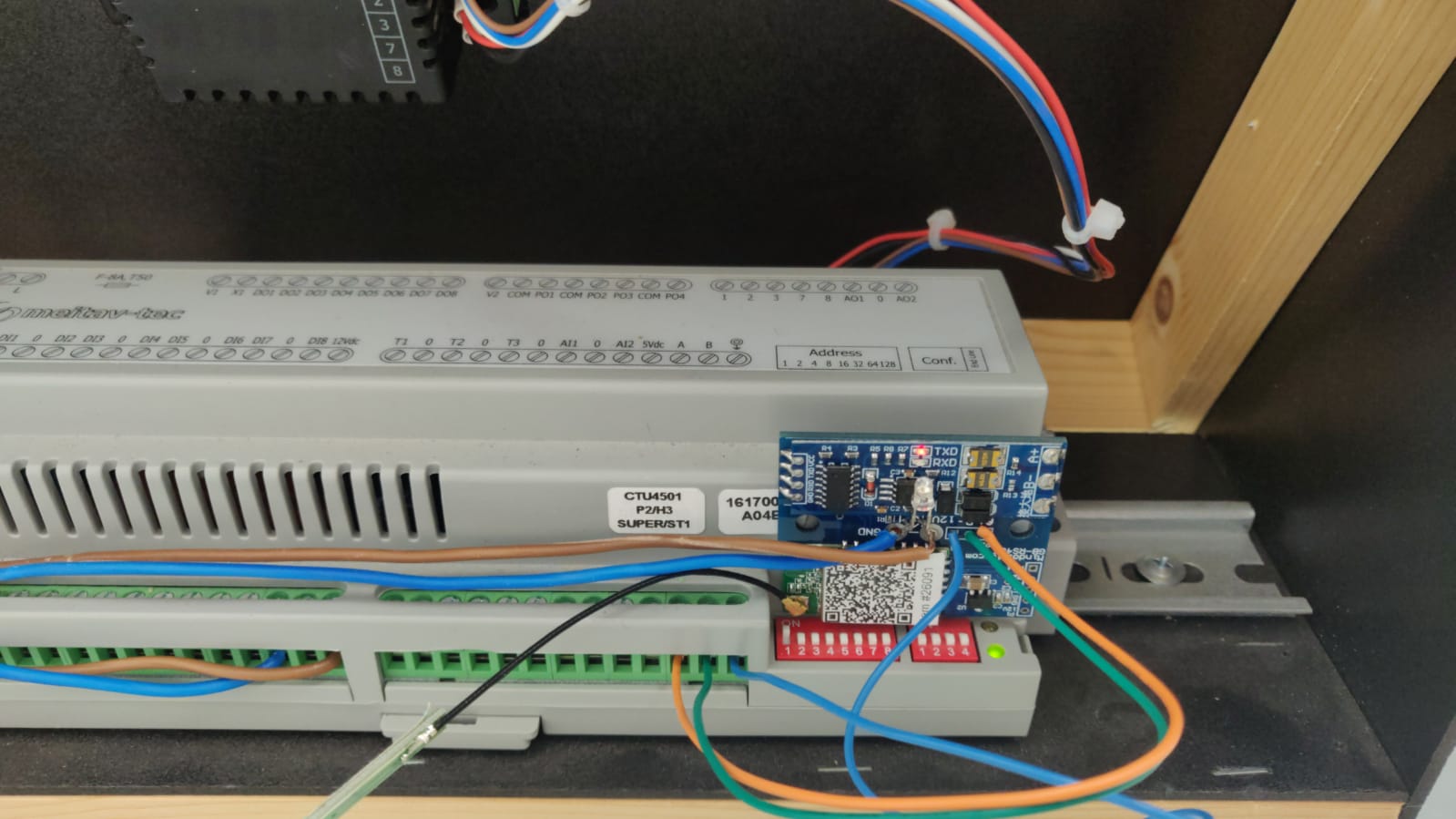
MindoLife provides an end-to-end software & hardware solution that integrates unique security protocols and network management to deliver the safest springboard for your IoT products and solutions
0
2
- Weeks To reach the demo milestone
0
6
- Weeks To reach the MVP milestone
0
3
- Months To reach the production milestone
Build your Go-to IoT strategy
In the rush to develop or add IoT functionality, companies are neglecting to take into account all the potential security risks that come with devices that are connected to the Internet. The attitude is mostly: develop first, add security later. This is inherently wrong and costly
Using MindoLife reduces you time to market?
For those who possess the passion, creativity, and intelligence to operate in the IoT market, MindoLife’s SDK and API is the most innovative, robust and flexible IoT platform of its kind, simplifying and securing your development, while enabling you to bring even the zaniest of ideas to fruition.
Why choosing MindoLife for your products?
An advanced secured industrial IoT platform with unique features and added values
MindoLife’s industrial IoT platform equips your connected products with advanced features and huge customer added value.
Secured from day one
3rd Party Integration
Support low-power products
Scalable and robust Network
Advanced automation engine
Dynamic and modular